Clubhouse Data Breach: Which Users Was Affected
The clubhouse is an audio-chat-based social networking app. In this App, users listen to conversations, interviews, and discussions with interested persons on different subjects, much like listening to a podcast but live and with an additional level of exclusivity.
The clubhouse is an invite-only app. You can’t simply download and create an account from the app store. You must be invited to join an existing member, much like a real-life country or yacht club. But make it virtual, the real-world elitism.

You choose themes of interest, such as technology, literature, business, and health. The more information you provide about the app, the more conversation rooms and people you may follow and join the app.
The conversation room is like a conference call, except there are some individuals that talk and listen. And, like a phone call, the room is closed once the discussion is finished. In contrast to Twitch – where videos broadcast live remain to view and return to the platform and live audio conversations disappear in conversation rooms.
How users get in
For joining, an existing user must send an invitation from their app to set up an account. You will see a link with your phone number if you’re invited, which leads you to the registration page in the app.
However, users of Clubhouse cannot simply send a call to anybody wanting to join. Only two invitations are offered to existing users at first.
Clubhouse Analytics
The hackers of clubhouse develop a fake Android app in the name of Clubhouse to target malware to users in a SQL database of 1.3 million. Clubhouse records have been released free on a prominent hacker forum. They are not only those who were in the clubhouse hack but also the contacts of their friends who were in their phone book.
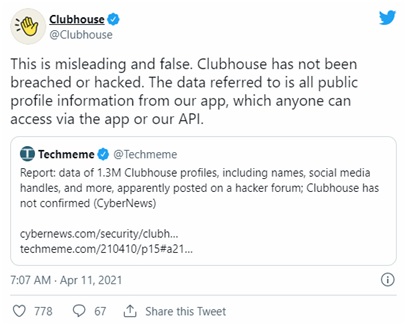
Statement of the official Clubhouse representative
Clubhouse released a statement on social media after the incident stating that this is only a rumor; they had not suffered a breach of their systems. The company also said that the clubhouse records are available to the public already, and “anyone” may access them through Clubhouse API.
How users affected after clubhouse hack
By performing targeted phishing or any other kind of social engineering attacks, threat actors targeting clubhouse users may utilize the data from these stolen files.
The SQL database on the hacker forum simply includes information from the Clubhouse profile that we have found no sensitive information like credit card numbers or documents in the threat actor’s archive. This means simply a profile name and the user’s links to other social media accounts found there.
But it may be sufficient to cause actual harm by an appropriate cybercriminal. To build comprehensive profiles of their prospective victims, dedicated criminals may integrate information in a stolen SQL database with previous data breaches. They can conduct phishing and social engineering attacks using these details much more convincingly or even perform identity theft against individuals whose information is disclosed on the forum.
How to protect yourself from the data breach
Preventive measures, such as carefully checking your account (and early filing of taxes), may avoid or reduce the risk of frequent exposure to online data. “The simple things are often the most important,” Pollack remarked. Here we will discuss the tips for protecting yourself from data breaches.
1. Do not enable third-party Access
Once you’ve enabled other parties to access your data, they can use your data for any purpose. Look at the privacy settings of your account and check if there is an option not to access certain applications or websites, then disable access to those applications or websites.
2. Use strong passwords
Use strong passwords, particularly on financial accounts. Rethinking internet sharing or limiting access to your public social media sites. A thief may utilize the information on your accounts to answer security questions (what was your first name, the maiden’s name of your mother, etc.)
3. Avoid using public Wi-Fi
Avoid using public Wi-Fi. Fraudsters may easily access your devices if you are using public Wi-Fi. And if you want to hide IP online, then you have to use VPN. VPN will mask your IP address, and you can access the internet as an anonymous person. If you are searching for an amazing VPN company, you can try VeePN. VeePN is one of the great VPN providers, you can ask them for a free trial online, and I am sure you will love it.
4. Avoid phishing email and spam calls
Scams, such as phishing emails and spam calls, which are trying to get you to provide your financial information, are the most frequent method of obtaining your information for hackers.
Data Leak Check
Companies are legally obliged to inform users of data violations, but such disclosures frequently occur via vague public announcements, and before that, customers are kept in the dark. Fortunately, security researchers maintain comprehensive archives of previous data points that you may use to verify for an infringement.
HaveIBeenPwned.com, a security analyst Troy Hunt database, is one such resource. With over 10 trillion accounts compromised in previous breaches, you may input your email address and cross-references to it to discover whether or not they are “pwned.”
Passwords are revealed in data violations in certain examples as well. The website of Hunt also offers a password search to help individuals understand whether or not hackers have ever handed over their password.
Conclusion
Recently a Cache of 500 million LinkedIn accounts was released online, with 533 million members in 106 different states being hit hard by Facebook previously, revealing Personal Identifiable Information (PII) including names, email addresses, phone numbers, etc.
Clubhouse users are advised to avoid suspicious communications and foreigners’ connection requests and are also instructed to change the passwords of the account promptly.
